On June 29, 2007, the first iPhone was released. It revolutionized the mobile phone industry and gave birth to smartphones that soon became more powerful than most computers available in 2007. Although the iPhone was the biggest breakthrough for smartphones, it was actually Android that bought the smartphone to the masses and gave them the freedom to do what they wanted on their phone.
Ever since the release of HTC Dream (T-Mobile G1 in the US) in late 2008, we have had rapid innovation in the mobile phone market. So much so that the HTC Dream would be completely useless to anyone who wanted a smartphone in 2019.
Just like the HTC Dream and the original iPhone, the mobile security measures that people used to protect themselves from malware, viruses, and invasion of privacy have also become obsolete a decade later. Not only has the malware become extremely intelligent, but spyware now allows any hacker worth his weight to spy on thousands of people.
What Is Mobile Device Security?
The term mobile device security can be defined as a way of delivering full protection of data on portable mobile devices as well as to the network connected to them. Some of the common portable devices that work within a given network are smartphones, tablets, personal computers (PCs) etc.
Is Mobile Security Important?
Today, mobile security plays a very crucial role in our day-to-day lives, for instance, more than 50 percent of the total business systems are mobile devices. This further promotes the use of IoT (Internet Of Things) technology in order to achieve the required level of mobile device security.
Best Ways To Protect Your Phone In 2019
Due to this, mobile security mechanisms have also evolved. So, let’s go ahead and take a look at how you can protect your phone in 2019:

1. Use a VPN
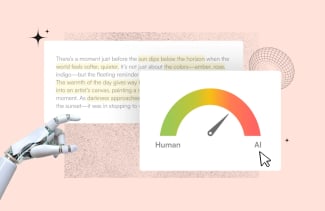
Using a VPN is probably the first thing you want to do. Due to the fact that the main functionality of your smartphone is to connect to the internet and have your applications interact with it, the internet is the main way through which your privacy can come under threat.
A VPN solves this problem by having your entire traffic routed through one of its secure app servers and encrypting all the data you send and receive. This means that even if someone is able to get access to your data, they will not be able to view it.
Another major problem that VPN solves is the mobile device security threat of public Wi-Fi. Since all your data is encrypted and the VPN makes sure it is not possible for you to have any DNS or IP Leaks, you will be able to use public Wi-Fi without worry.
Now answering your question to ‘why use a VPN’. You can choose a VPN for Android devices from this list. These VPNs will also work with your computer as well as any other mainstream portable devices that you have. Using any of them will ensure complete anonymity and privacy when browsing the web.
2. Delete Apps That You Do Not Need
The Google Play store is by far the biggest marketplace for Android applications, and it is very easy to get lost in it and download way too many apps than the ones that you actually need. While it may seem like these applications do not have any negative consequences and you can just leave them on your phone, which is not the case.
Many of these applications have privacy policies which allow them access to various different directories on your phone including your photos, contacts, and documents. While the chances of an app actually farming data from your phone are quite slim, it only takes one app to do the damage.
It is best to uninstall applications that you are not using anymore and any applications which are not providing you with any utility as well. This way, there will be fewer intrusions for you to worry about. It is not possible to protect your privacy through a VPN or other software from these apps as it is ‘you’ who gave them permission to access your data.
3. Get An Ad-Blocker
Ads may seem particularly harmful and useless, but they are much more than that. If you click on an ad when browsing the internet, there is a fair chance that you will be taken to a domain which harvests as much information about you as it can.
Using an ad-blocker will make sure that it is impossible for you to click on an ad since no ads will be visible. There are many different reputable ad-blockers currently on the market, and you should select one that not only serves your purpose but is also priced well. This is also one of the easiest ways to block all ads that are annoying you!
4. Enable Two-Step Authentication For Your Google Account
Since your Google account is the main way through which you set up your Android phone, it is best to protect it as well as you can. Your Google account’s password can be stolen, but it will be impossible for a hacker to access your account when you have Two-Step authentication.
When you use Two-Step verification, your phone will send a randomly generated code whenever an unknown device logs in to your Google account. This specific device will only be granted access to your Google account once you enter your authentication code.
You can easily set up your two-step authentication by following instructions from Google. Once you do that, simply test the process by logging in from a device that you have not used before.
Final Thoughts
It has been over 10 years since the release of the first Android phone, and the mobile device security landscape has definitely shifted. However, the good news is that you can still protect your device without going through much hassle by following the instructions outlined above. Once you have followed all of our tips, it will be nearly impossible for anyone to access your phone and your private information.
If you are interested in reading more such articles on the topic of mobile phone security and how to secure your phone then make sure you follow MobileAppDaily. To stay updated all you need to do is click on that ‘Subscribe’ button and never miss another important update from us.
Uncover executable insights, extensive research, and expert opinions in one place.