Science and encryption are used today to keep our most sensitive and personal data safe and secure from those who we don’t wish to access it. Today we have many sophisticated and refined tools that can be put to use in protecting our data. These tools not only keep our data safe, but they also ensure that even if it does fall into the wrong hands, only the intended recipient is available to read it.
We have all grown used to seeing encryption portrayed as an almost mystical form of art. In the realm of film and television, encryption is the Deux Ex Machina with a seemingly endless capacity for solving or exacerbating issues, as the story calls for.
To understand the murky world of encryption, and why this often esoteric, impenetrable even, subject matter is portrayed in the way it is, it is essential to understand what encryption does, and why it is so crucial to even the most basic consumer devices.
Before we look in any detail as to why encryption is so important, especially in the context of a modern smartphone, we need to make sure that we know what “encryption” means. Encryption can be something incredibly simple, or something mind-blowingly complex. Yet, the underlying concept remains the same. Let’s dig more about encryption.
What is Encryption?
Encryption is pretty simple to define: it is the process of making something readable or viewable so that it can only be read, viewed, and understood by the intended recipient. This process of taking data and making it understandable again is called decryption. The intended recipient of a piece of decrypted data will be given decryption instructions. But it is the malicious actors looking to gain access to data they aren’t authorized to view that cause issues.
In its simplest, and oldest, forms, data encryption involves nothing more complicated than some form of letter substitution. Substitution, sometimes known as a ‘cipher substitution,’ works like algebra. The sender and recipient will have an agreed-upon key. This key will show how the usual alphabetical characters and symbols have been switched around. So now h=p, e=©, l=>, and o=t. So “hello” becomes “p©>>t.”
Needless to say, modern electronic devices use much more sophisticated methods. Humans are capable of deciphering simple substitutions, but computers find them laughably primitive.
Why is Encryption Important for the Mobile?
Here’s why you should encrypt phone.
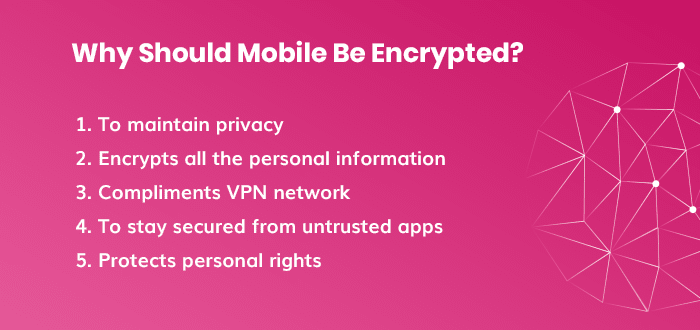
1. Privacy
The privacy concern is the big one. Anyone who can lay their hands on an unencrypted file can read its contents. Even with an unknown file type, a lack of encryption would make it possible to find out what it said.
2. Protection by Default
Having all your mobile storage encrypted is definitely helpful in preventing anyone who steals your phone from stealing your identity. But, what about the stuff you haven’t encrypted? A thief can pull those files from your unencrypted phone without even having to power it on and log in.
For this reason, all modern smartphones and all Windows machines since Vista encrypt their hard drives automatically when they are powered off. Until the user turns the device on and enters their password, the files are virtually impossible to decrypt. This means that the average user benefits from strong encryption by default.
3. Virtual Private Networks
A virtual private network (VPN) is an essential tool for anyone who wants or needs to keep their Wi-Fi communications secure. A VPN creates a secure encrypted communications channel between your device and the internet. A VPN can be used by businesses to keep information encrypted until it reaches its destination. Without the strong encryption offered by a VPN, many businesses would have to reconsider their operations.
4. Trustable Apps
We all hand over vast amounts of sensitive and personal information to app developers. Whether this is to allow the app to function as intended or not, we would all hope that any data stored about us is kept encrypted. Otherwise, any other app developer could slip in and take a peek at the unencrypted information.
5. Personal Rights
We mentioned privacy earlier, but relatively few countries have enacted any legislation or regulations designed to protect digital rights. If a file is unencrypted, anyone can access and view it. However, with an encrypted file, the consent of the data owner is required to access it. Encryption means you can store personal information on your device with confidence. Even governments have been defeated by the strength of modern encrypted smartphones.
Final Thought
The phone encryption is not new in the mobile industry and encryption has become an inevitable part for all the smartphone manufacturers. From saving your data to get compromised to making your personal details super-secret, mobile encryption can do it all for you.
Now, as you are well aware of the significance of the encrypted phone, get all your mobile devices encrypted and shield your data from any unwanted breach. For more information on the data and mobile encryption, get in touch with us by commenting below.
Uncover executable insights, extensive research, and expert opinions in one place.