Editor’s picks
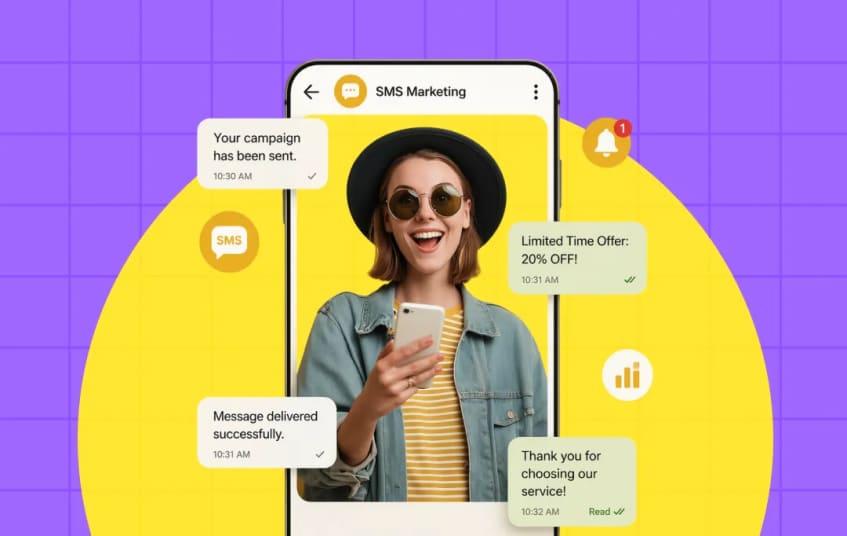
How Much Does SMS Marketing Cost in 2026? Complete Pricing Guide
Understanding the financial side of mobile communication is a major part of your overall growth plan. This guide looks at how much SMS marketing costs by breaking down the parts that make up a
Freshly Published On MobileAppDaily
Opinions From Industry Veterans
View All
Why 90% of Mobile Apps Fail at Retention (Spoiler: It’s Usually Not the Product)
By Devjeet Director, Conversion Perk
Will AI Replace Developers? No, It Will Redefine the Role
By Prahalad Madepally Sr Engineering Manager, WaveMaker, Inc
Why Your AI Project Will Fail - An Expert Opinion from Maurice Adam Weber
By Maurice Adam Weber Founder, Crebos Online SolutionsJoin our Newsletter?
Subscribe Now to our no-spam newsletter.