
In this digitized world, mobile apps have virtually become part of our lives. From the alarm clock to booking a cab for office and from ordering grocery in the evening to late night texts, we all are covered under the umbrella of mobile apps. So, it becomes very crucial that we trust the platform on which we spend more than half of our day.
Moreover, in the age of data breaches and cybersecurity threats, the possibility of a mobile app hack remains a dire possibility. Many of the businesses back out of using a mobile app to assist them in their day to day tasks, just because they are not sure about the adequacy of mobile app security. Moreover, with the addition of high-speed internet and spurt in the number of hackers have only complicated the whole process of securing the mobile app and mobile device security.
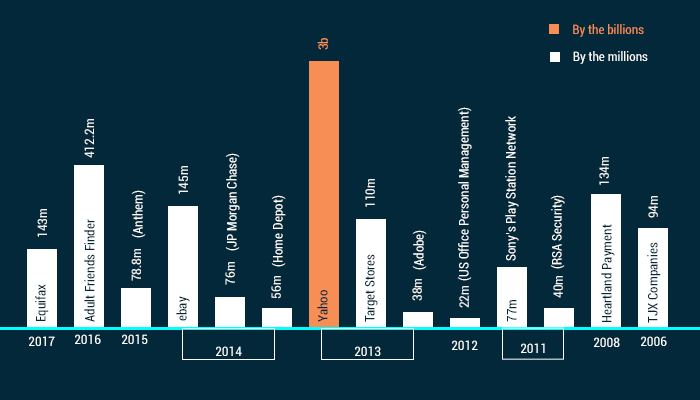
Biggest Data Security Breaches
Bleeding Data
You must have come across the instances where hackers got hold of personal details of customers of a company or brand. It is one of the most common security failures in mobile apps. In 2016, the personal information of almost 57 million Uber users and 600,000 drivers were exposed by the cybercriminals.
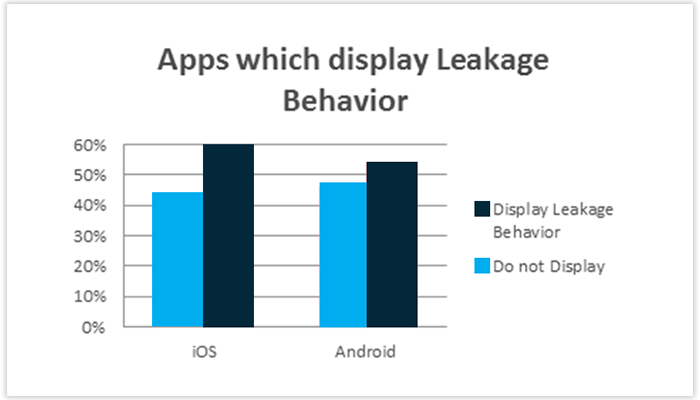
These types of data leakage take place when the information is stored on the unsecured servers. The reasons for the security breach are as follows are:
- Bugs in the operating system
- Irregularities from the developers’ end
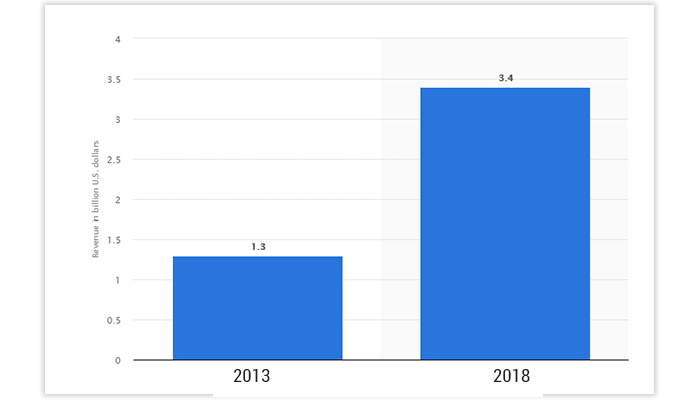
Global Mobile Device Security Software Market
The following graph represents the global mobile device security software market revenue in 2013 and 2018. If we look at the year 2013, the market volume of mobile device security software was $1.3 billion and going forward, the projected growth till the end of this year will touch to $3.4 billion.
A mobile app lacking all the relevant security tools will be a feast for cybercriminals to exploit. So, you need to secure your mobile app and keep its content relevant at the same time.
How To Fix The Issue?
With the changing trends in the codes and languages to develop an app, apps are designed to be more steady and secured. Even the companies are offering security courses to their staff in order to tackle any vulnerability.
Going by the stats, it cost around $1000 to find a bug in the app codes and $4,000 to fix that glitch. So, it’s always better to take the initial measures rather than finding the vulnerabilities later on.
There are different levels of security that you can follow. Here are some:
1. Bring In Mobile Security Standards
Every organization has set guidelines related to app development. Even if a company outsources an app development company to get an app designed, they form their own guidelines on which the app needs to be developed. Sadly, the guidelines hardly cover much of the details on security and rather focuses on other parts.
Therefore, it becomes crucial to comply with security standards and guidelines while developing an app.

2. Engage A Professional Security Team
If you are serious about your app’s security, get yourself covered with a professional team of developers or coders who has expertise in taking on such projects. By doing so, you will be securing your app and the data of your clients or customers from the day one.
Also, aks your security team to come up with a blueprint of their plan, so that, you should be in the loop of whatever they are doing. Furthermore, it will aid the security team also, in case, you get some changes done to your app. A team of professionals can also design codes that are tamper proof.
3. Shield Your Code
You need to secure your codes at all cost because of most of the time. It is the coding of the app that is being compromised by the malware attacks, and then the hacker takes advantage of the loopholes.
There are certain apps also whose codes are publicly available and it puts the app security in more danger of getting attacked. Usually, hackers copy the codes of the app and then create other copies of that app, coupled with malicious codes that can’t be spotted by everyone.
You can avoid getting into such type of vulnerabilities by getting along with a set of professionals that are wise enough to handle such situations.
Common Mobile App Security Issues
- Unintended Data Leakage
- Poor authorization
- Improper session handling
- Broken cryptography
4. Design Review
The apps are getting more complex day by day, and with the introduction of the mobile channel, the things have got more complicated now. In order to support new mobile channels, some apps modify the current security infrastructure. And for adding a mobile channel, you need to rework on the design and the architecture, taking threat modeling into account.
If we see it from the other side, by doing so, we can uncover any bug or threat that may have crept into the app code and this way; we can better the app.
5. Robust Authentication
Authentication means logging into an account with a password or OPT (One-time password). It’s the user who has to set the password for their app but being the developer or the owner of the app; you can encourage your user to use a strong password that can’t be breached easily. No doubt, a weak security authentication method of an app can also land you in trouble.
To help the users, you can design the app in such a way that it should accept only alphanumeric passwords that can be renewed with the help of OTP. Another method of saving the app from the unauthorized breach is dual-factor authentication, which will make the user login into the app with a code that is usually sent through text or email.

Don’t forget about the biometrics like fingerprints, face ID and retina scan authentications. All these methods are taken as the most secure way of authentication.
6. Manual Verification
It is always a wise idea to check the app through manual verification. It will help you to directly get in touch with the security issues that may have crept in the codes of the app during development. Do remember, before jumping into the manual verification process, know about the complexity and size of the app because you will be required to verify through iterative code reviews and penetration testing.
Organizations must engage mobile verification experts to work alongside internal teams. Companies should have an eye towards building a strong testing group from within.
7. Use Encryptions
Data encryption is usually used to convert the information into codes, which can’t be encrypted easily. By doing this, you can save all the data of the customers; be its name, address, phone number or banking details. Even if the cybercriminals hack the information, the possibility of decryption remains very thin.
The need of the data encryption is a must for those apps which regularly exchange data with the customers. For instance, an app that let the user know about the nearby locations can be hacked by the cybercriminals to track your location or know about your interests. Therefore, adding encryption in such an app will secure all the information of the customer.
Key Takeaways
- Always layout guidelines for your app
- Stick with professionals
- Encrypt your app data
- Use high-level authentication methods
- Don't make your app code public
- Keep testing your app for bugs
Uncover executable insights, extensive research, and expert opinions in one place.





