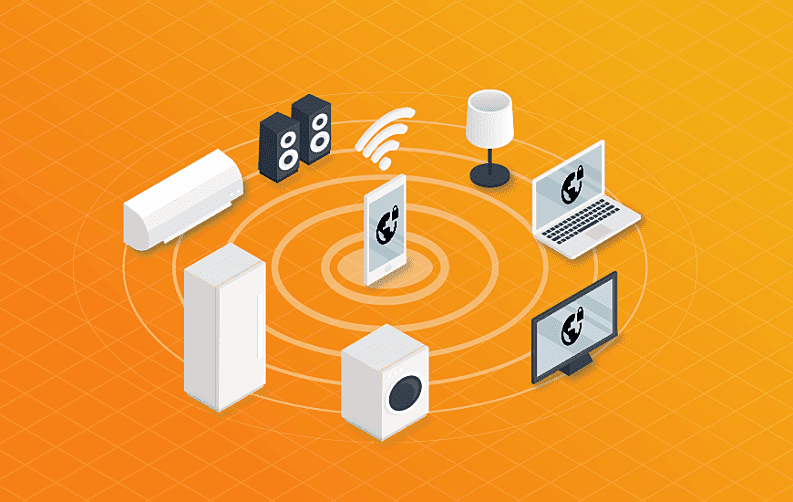
The Internet of Things or IoT has enabled communication between robots, automated driving, and smart homes. This concept has become a phenomenon with a wide variety of potential for the future. IoT is still not completely understood, yet it is consistently changing and evolving.
The majority of the experts agree to the fact that the Internet of Things has not yet reached its full potential. The not too distant future will most likely reveal innovations, concepts and better security for the internet. This may help prevent the loss of data to hackers.
Currently, the best form of available internet security is a VPN or a Virtual Private Network. It provides a great deal of protection for online browsing. VPNs can also secure any devices based on the Internet of Things.
What is a VPN?
A virtual private network is a specific kind of technology enabling the user to establish a secure channel to access the internet. This helps prevent anyone from stealing data, hacking or using the connection for eavesdropping. There are a lot of credible VPN apps and services offering subscriptions to both businesses and consumers. Once the VPN service has been established, the connection cannot be intercepted by a third party network.
If this attempt is made, all that will be seen are incomprehensible and scrambled characters. It is due to the encryption employed by a VPN. A VPN also enables the user to hide their location. This prevents anyone from knowing the exact location of the device. For additional details about VPN, you can check out VPN Vanguard, one of the top sites for VPN.
Securing Devices Using the Internet of Things
There are a lot of IoT devices accessible to the public. The majority of these devices have very little computing power. This is because no additional capacity is necessary for their operations. A VPN service establishes a type of link between the IoT device and the IoT app server.
It makes sure that the device is completely protected while it is operating. The VPN service also prevents any opportunities for the connection to be hacked. For more information, click here.
IoT Security Prevents Numerous Issues
Unfortunately, not everyone has taken the necessary steps to protect their IoT devices. An excellent example of the damage it can wreck is the Michigan University case. The campus students hacked into their city's traffic lighting system and changed the colors the traffic light displayed at any time.
This action had the potential to cause serious harm. Since they were able to hack into the lighting system with apparent ease, it stands to reason they could access other targets as well. For more information, click here.
When a VPN is used in combination with additional security measures, this type of action becomes much more difficult because the connection becomes encrypted. The camera would have been locked down by the VPN. This means communication could only be established with a recognized IP address.
It is the best way to help prevent any outside access. A VPN also enables the user to retrieve any data regarding their IoT device and there are no limitations regarding the network protocol the user chooses. For VPN services, click here.
Another good example of the capabilities of a VPN is a mechanical engineering company. This company theoretically manufactures wind turbines for distributions across the globe. If this company used built-in SIM cards as opposed to a VPN, they would be able to run tests when a problem occurred to locate and resolve the issue.
When this technology is combined with a VPN service, the company could make certain no unauthorized individuals to access the turbines remotely. Any workstation with an authorized connection to the VPN could easily view and act on the results. For some good ideas regarding a VPN service, click here.
VPN Protocols for IoT Security
There are a lot of VPN protocols consumers and businesses can choose from. There are two that are both extremely popular and highly recommended for IoT devices.

These protocols are:
- IPSec (Internet Protocol Security): IPSec enables the user to use a remote device to establish a tunnel using a central server. It was created to use private and secure communications through the internet and uses cryptographic services.
Also, it is an excellent choice for large businesses and firms requiring multiple layers of security and numerous peers. A static IP address is required to use this protocol. A wide variety of technical resources are also required for implementation. If the data transfers are of an extremely sensitive nature, this is the best protocol to use. This will protect every device secured to the IoT.
- OpenVPN: The second protocol is OpenVPN. This option is appropriate for both consumers and small businesses. It uses a security protocol referred to as SSL/TLS. Having an SSL certificate for your website enables customers to use a shared key to authenticate one another. This protocol requires the users to have a connection to the OpenVPN server. Once this connection is established, the users will have no difficulties safely accessing the internet while protecting their IoT devices.
This kind of protocol is an excellent choice for users with either a dynamic or static IP address. The majority of VPN services are currently providing the required software. This will provide premium security to SME's as well as the flexibility found with open-source software. This protocol is also a good way to protect IoT devices. To VPN provider reviews, click here.
The Bottom Line
The use of an IoT device is indeed not a bad choice. This being said, the lack of adequate security can jeopardize both security and privacy. The best security currently available for IoT devices is a reputable service. It will make every single IoT device fully protected. Additionally, it provides a secure communication channel between the device and the user.
For more information on VPN services, get in touch with us and we will assist you in every possible way.















